Featured
Latest News
Grandparent’s Rights: Filing for Emergency Custody Amidst Family Crisis
In the whirlwind of family crises, the stability and well-being of children often become a primary concern. In such turbulent times, grandparents can play a pivotal role in ensuring the safety and security of their…
The Top 5 Power Over Ethernet (PoE) Powered Devices
In today's economy, businesses continue to look for ways to save money while fostering growth. One of the more popular approaches, especially in light of the current digital advancement, is a buildout of the IT network…
Achieving Precision and Quality: The Art of Medical Plastic Injection Molding
Key Takeaways: Medical plastic injection molding allows for the production of intricate and complex plastic components with precision and efficiency. Selection of appropriate materials is crucial in medical plastic injection…
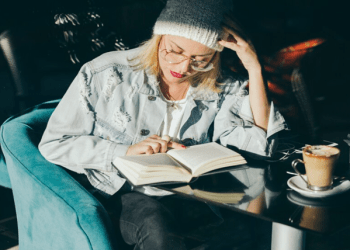
The Art of Capturing Memories: A Guide to Writing Your Life Story
Key Takeaways: Your life story is unique and writing it down preserves your personal history, provides closure, and offers wisdom for future generations. Sharing your personal narrative can create empathy, inspire others, and…
Making the Most of Your Life After a Debilitating Injury
Adapting to life after sustaining a debilitating injury can be challenging. These injuries often result in long-lasting or permanent impairments that can heavily impact one’s daily routines. It is a process of change that…
From $10 to Naira: How Bitcoin is Transforming the Value of Cryptocurrency
Bitcoin, the world's first decentralized digital currency, has been making waves within the monetary market since its inception in 2009. With its promise of safe, borderless transactions and a restricted supply, Bitcoin…
Can Accurate Medical Transcription Improve Healthcare Outcomes?
Medical transcription helps create a patient's medical history that lays the foundation for future cases of similar instances and serves as a reference for physicians. It helps the doctors to assess the current physical…